Background
I have had a server with OVH for the past several years, and one of the things that took me many months of research, as well as trial and error, to get right was my IP address configuration for virtual machines. The documentation available from OVH has been consistently lacking these past few years on how to properly configure it.
Debian \ Ubuntu systems will add to the complications, because they do not agree with the necessary configuration. If you try to add it traditionally, just by editing /etc/network/interfaces, you will most likely end up with no default gateway when you’re all said and done, and your connection still won’t work.
For the first few months I was with OVH, I was launching my networking through a shell script in a cron job, because configuring it with /etc/network/interfaces just didn’t seem possible.
What You Need For This Guide \ Assumptions About Your Setup
1. A dedicated server on the OVH network. This guide has been tested in the Roubaix datacenter, Gravelines datacenter, and the BHS datacenter.
2. A virtualization platform installed, and a virtual switch bridged with your network interface. I have been using VMWare, and a vSwitch bridged with my eth0 interface. This guide should be applicable to any virtualization suite (Xen, OpenVZ, etc) as long as your networking is bridged.
3. A Debian \ Ubuntu VM. You can apply the knowledge gained from this guide to other operating systems (eg. CentOS) but the configuration will be different as the files are located in different places and are parsed differently.
4. A purchased IP range. You can purchase IP addresses from OVH in your Manager Panel.
Gather Your Information \ Initial Setup On OVH Side
1. Your dedicated server’s Main IP will be needed for this guide. Say, for example, your main IP is 123.4.5.67.
2. Your dedicated server’s Gateway IP will be needed for this guide. On the OVH network, this is the first three octets of your main IP, ending in 254. For 123.4.5.67, the gateway is 123.4.5.254.
3. A Fail Over IP Range registered with OVH. You can register any size IP block, and you can pick any IP from the block. Say for example, you bought 5.6.77.8/29. All of the Fail Over IPs are usable at OVH, so you have available all 8 IPs from 5.6.77.8 to 5.6.77.15 for use for your VMs. You can purchase an IP block from your Manager Panel.
4. A Registered VM MAC Address associated on OVH’s routers. Without this step, your connection will not work. You can register VM MACs in your Manager Panel.
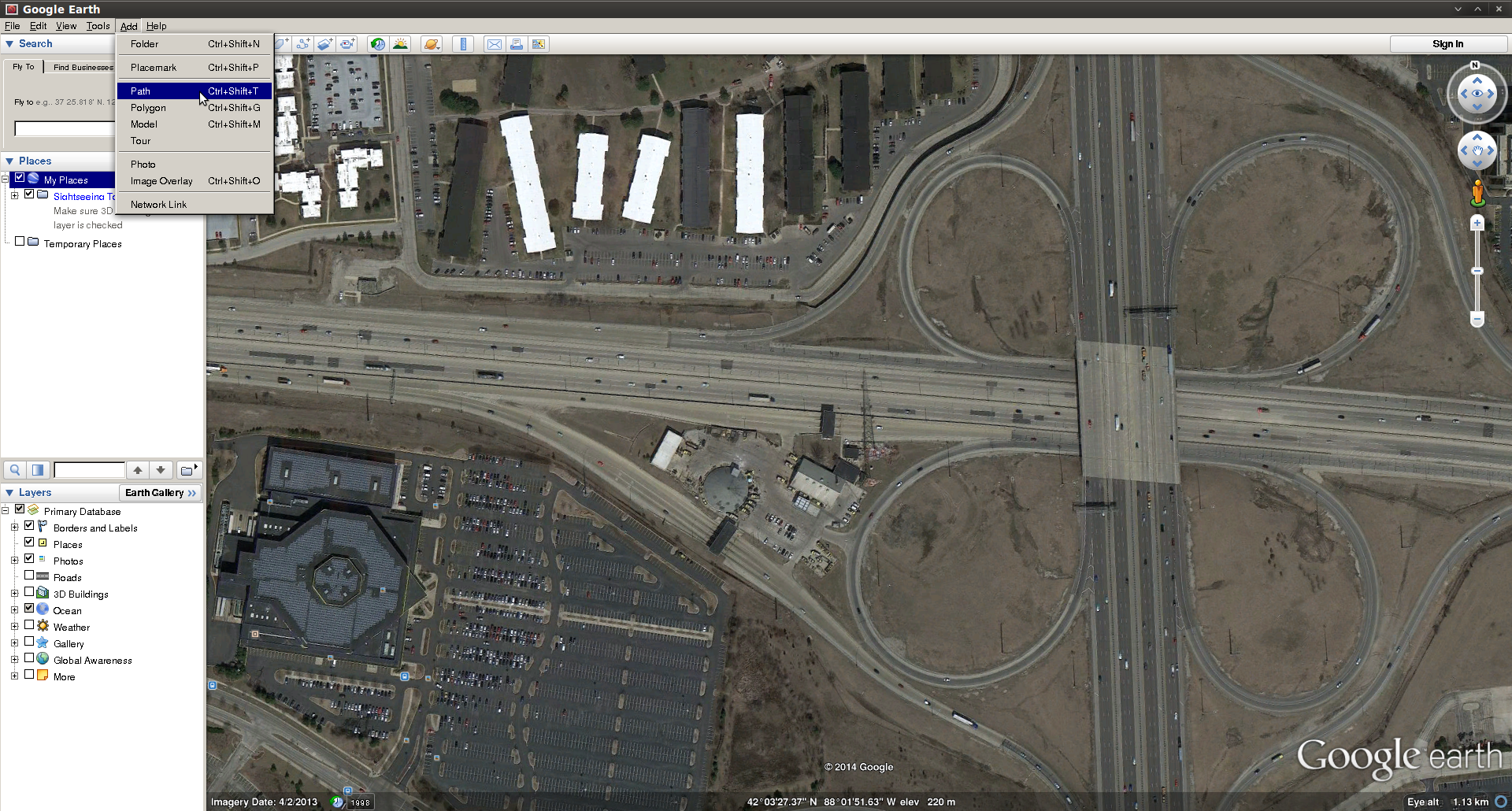
How To Register A VM MAC Address
In the new OVH Manager panel, you can register a VM MAC address by going to the “Manage IPs” page, clicking the gear icon next to the IP(s) you want to assign to the VM, and clicking “Add A Virtual MAC”. You can choose an existing MAC address if you are assigning more than 1 IP, otherwise OVH will assign a new MAC address to you, and you will edit your VM preferences so your network interface has this MAC address. Make sure you select the MAC address type “VMWare” if you are using a VMWare server, as this will generate MAC addresses which VMWare will accept. You can use type “OVH” for any other virtualization platform. The “name of virtual machine” field is just for your notes, and can be anything.
Operating System Installation
Install Debian \ Ubuntu to the VM, from a full install media. Do not plan on doing a network install, as this guide does not cover how to make the OVH networking functional during installation; only after installation. Skip the step for setting up networking during the installer, leave it unconfigured.
Setting Up /etc/network/interfaces
Now that you have your operating system installed, you are ready to configure your /etc/network/interfaces file. This guide assumes that eth0 is your Internet interface. I will use IP addresses from the example above under “Gather Your Information”. Do not use these addresses, substitute your own IP addresses.
auto eth0 iface eth0 inet static address 5.6.77.8 netmask 255.255.255.255 broadcast 5.6.77.8 post-up route add 123.4.5.254 dev eth0 post-up route add default gw 123.4.5.254 post-down route del default gw 123.4.5.254 post-down route del 123.4.5.254 dev eth0
A few things to note, for anyone asking any technical questions about what I just did above:
- You should choose 1 IP address from your IP block. If you want to add more, see the further instructions below. This IP is the Main IP of your VM.
- Regardless of the size of your block, you will treat the IP address as a /32 with a netmask 255.255.255.255.
- Because you are using a /32, the network\broadcast IP is your IP.
- Your default gateway should be the same as your dedicated server’s default gateway. DO NOT try to use what should logically be the gateway IP for your IP block, and DO NOT try to set your dedicated server itself as the gateway. The IP block is irrelevant, the gateway is always the dedicated server’s gateway IP.
- The routes have to be added this way, because the configuration is not valid. The gateway should not be reachable from this network range, because it’s a /32. However, the gateway will be reachable anyway, and adding the routes this way should work.
DNS Resolution
You will also need to edit your /etc/resolv.conf to put a DNS name server in there, otherwise your server will be able to ping other IPs, but it will not be able to resolve DNS. You can just put a line in there, like this line which uses the public OpenDNS resolver:
nameserver 208.67.222.222
Want To Add More IPs?
Sometimes it is desirable to have more than one IP address on your server. You can easily add additional IPs from any IP block as an alias IP. You don’t need to configure any additional gateways, because the gateway is always your dedicated server gateway. You can purchase as many IP blocks as you want, and assign them all this way, it doesn’t matter if they are totally different IP ranges. In the example below, I will add 2 additional IPs from the IP range I used as an example, 5.6.77.8/29.
auto eth0:1 iface eth0:1 inet static address 5.6.77.9/32 auto eth0:2 iface eth0:2 inet static address 5.6.77.10/32
Having Problems?
If you are having any problems, please review these items:
- First, reboot the VM to ensure that all of the networking changes you made are fully applied.
- Can you ping your default gateway? If not, did your route persist? Run “route -n” and see if the route is there. If it isn’t there, try adding it manually by running the commands in the post-up in /etc/network/interfaces. See if you get any errors.
- Did you configure DNS? Try pinging just an IP address, (eg. ping 4.2.2.1) and see if you get any response.
- Did you remember to register a MAC address, and did you change the MAC address for the VM? Run “ifconfig eth0” and make sure the MAC address shown matches what’s registered in your OVH Manager Panel.
Need Further Assistance?
As always, feel free to leave a comment below if you need any assistance. I will be happy to help!




Recent Comments